Reliable transport
Reduce telemetry loss and unstable delivery with stronger buffering, retry, and backpressure decisions.
IoT Systems Engineering
This page captures the IoT domains I work in most often: edge gateways, telemetry delivery, transport security, digital twin modeling, and the operational tooling needed to run distributed systems with confidence.
The emphasis is on production-grade systems where telemetry loss, insecure defaults, or weak observability quickly become real operational problems.
Expertise areas
Reduce telemetry loss and unstable delivery with stronger buffering, retry, and backpressure decisions.
Make message flow health, gateway behavior, and incident debugging visible enough to act on quickly.
Harden gateway-to-cloud communication with explicit choices around TLS, mTLS, identity, and defaults.
Buffering, retries, backpressure, and loss prevention from edge to cloud.
mTLS, identity, key handling, and hardening of gateway and backend components.
Metrics, traces, alerts, and incident debugging workflows that work in production.
Tradeoff-driven choices for protocol, storage, processing, and deployment model.
Detailed IoT Expertise
I work in detail with edge gateway software, secure telemetry ingestion, and resilient data pipelines. Typical delivery includes robust message handling, queue/buffer strategy, idempotent processing, and recovery patterns for unstable network conditions across distributed IoT deployments.
My implementation stack often includes Rust and Scala for system-level reliability, Java/Spring Boot for service ecosystems, and streaming infrastructure built with Apache Kafka. I also design operational observability using OpenTelemetry, structured logs, metrics, and alerting to reduce incident response time in edge-to-cloud environments.
On the security side, I help teams implement transport hardening and identity controls with TLS/mTLS, key and certificate lifecycle management, and secure defaults for gateway and backend components. This is typically aligned with compliance and governance expectations in critical systems.
Architecture Lens
Where does state live, what happens during disconnects, and how do messages recover without duplication or silent loss?
How are certificates, device identities, and transport guarantees managed as fleets grow and environments become less predictable?
Can engineers explain pipeline health, trace failures quickly, and see enough of the system to debug the next incident?
IoT Focus and Research
The strongest IoT work usually lives at the boundary between embedded constraints and cloud-scale expectations. That is where telemetry pipelines, gateway software, event-driven processing, and system-state modeling need to stay understandable even when the environment becomes noisy.
I publish and reuse architecture notes around IoT security, resilient edge-to-cloud delivery, protocol strategy, and long-term maintainability of distributed platforms. The goal is to turn difficult system tradeoffs into concrete engineering decisions, examples, and proof.
IoT Technical Domains
I help teams collect, process, and govern streaming telemetry from distributed edge devices. This includes protocol strategy, payload formats, buffering/retry behavior, schema management, and integration into processing pipelines for analytics and operational monitoring.
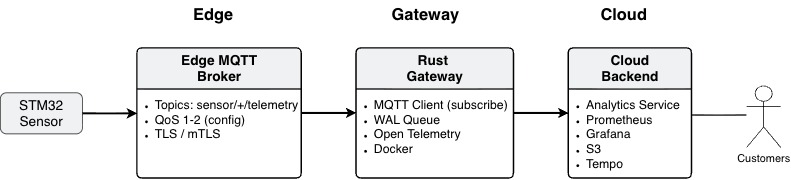
Typical implementation includes secure ingestion over MQTT, gRPC, HTTP, or WebSockets, compact schema choices for high-throughput streams, and topology design for filtering, joining, and aggregating data across multiple sources.
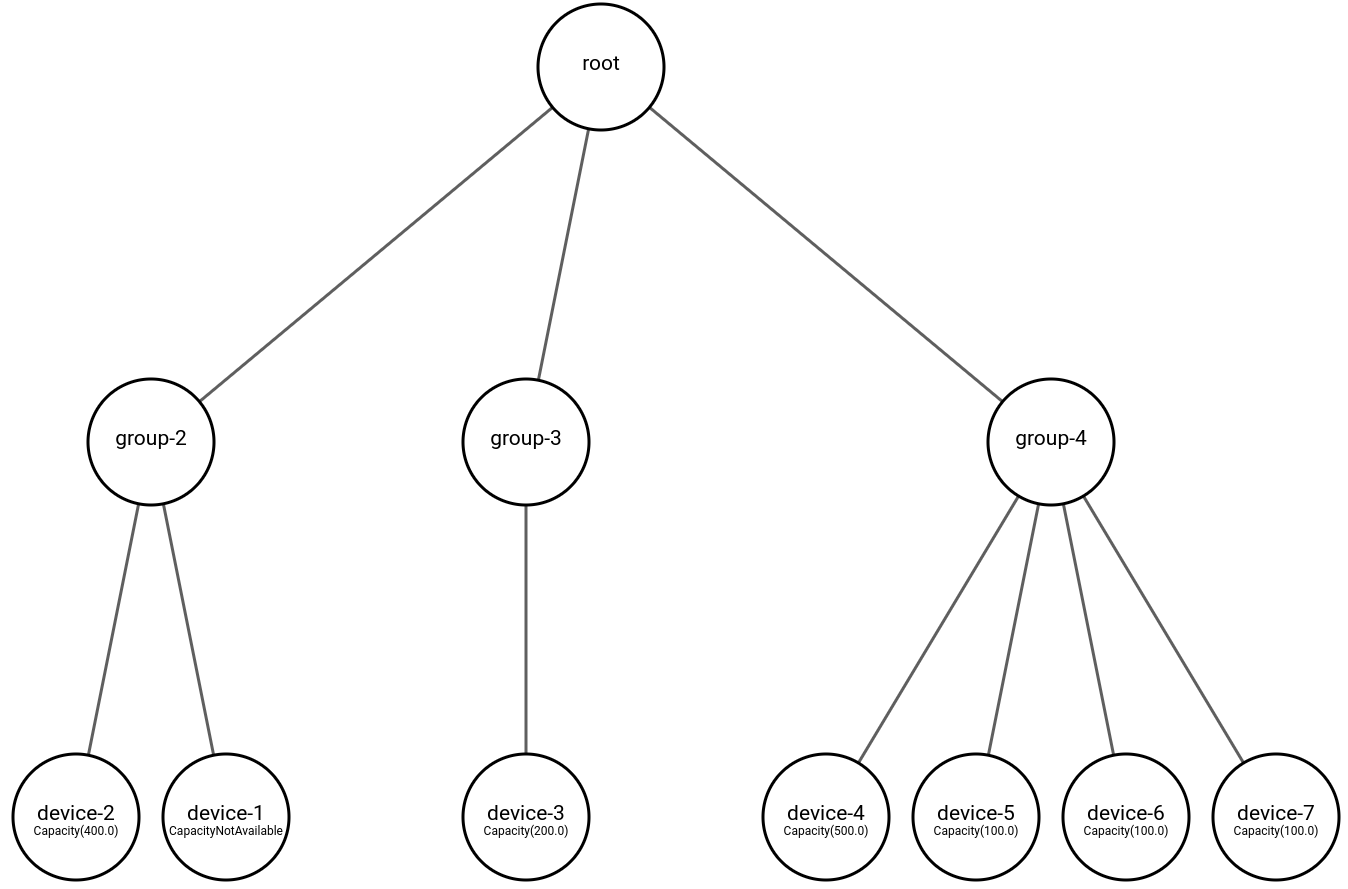
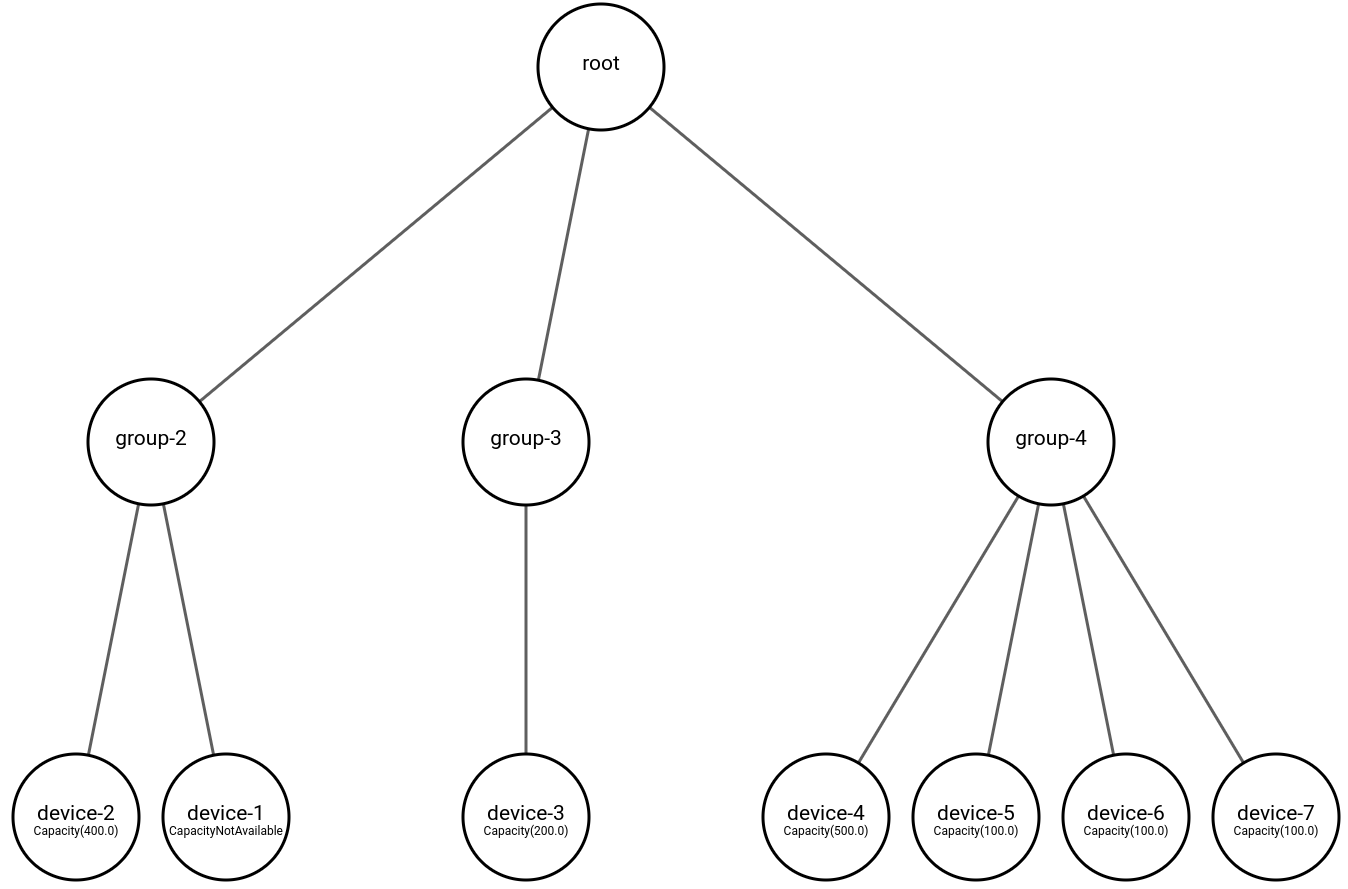
I design architectures that aggregate real-time measurements into actionable system views. This supports operational decisions, fleet visibility, and state-aware workflows in environments where many distributed devices must be coordinated reliably.
This often includes hierarchical entity models, message-driven updates, and robust handling of partial failures (timeouts, stale state, missing measurements) so operational decisions remain trustworthy.
Metadata is critical for fleet health, troubleshooting, and governance. I help implement metadata models and data quality controls that make it possible to evaluate connectivity status, ingest health, and signal quality over time.
Examples include device connectivity ratios, parsing/error rates, schema conformance, and pipeline-level quality KPIs used by both engineering teams and business stakeholders.
For mobile and distributed systems, I help integrate geospatial context into the broader architecture. This enables location-aware monitoring, route-level analysis, and operational decisions based on real-world device behavior.
Read more in my architecture deep dive: Design secure Rust IoT gateway architecture (edge to cloud).
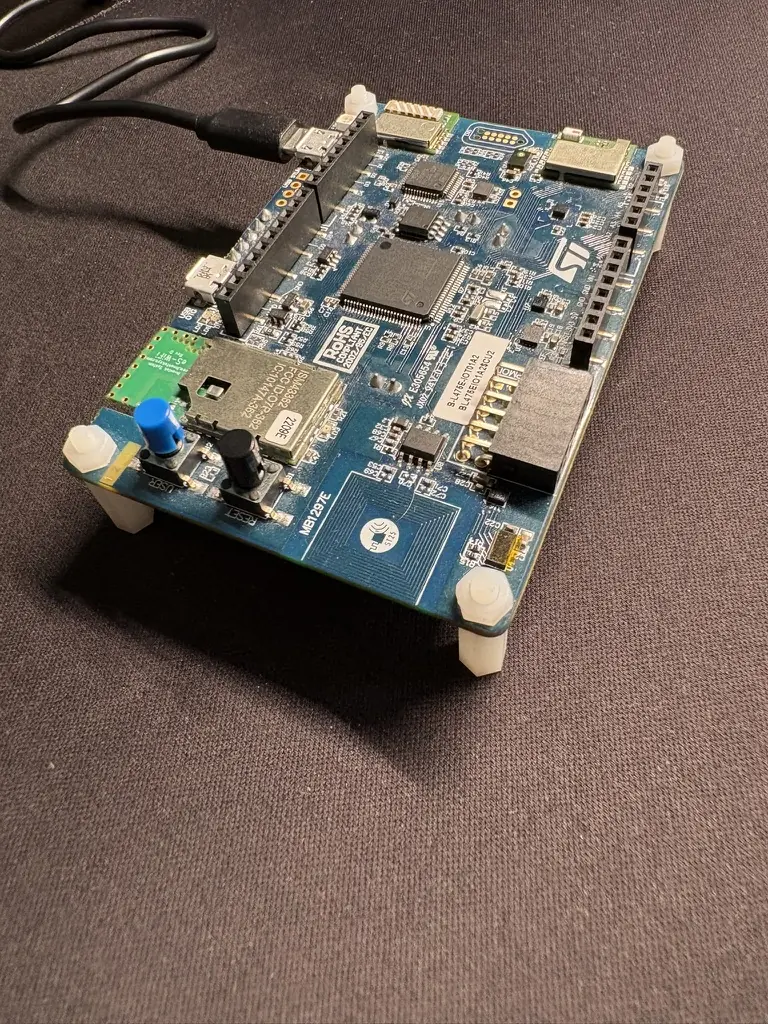
Visual Architecture Examples

Implementation Notes
In practice, IoT programs often fail due to weak boundary handling: unstable gateway behavior, inconsistent telemetry schemas, insufficient retry/buffering logic, and low observability across message flows. My work focuses on correcting these structural weaknesses early.
I help teams decide protocol strategy, data contracts, and security defaults that remain viable as device fleets scale and operational conditions become less predictable.
Typical outcomes include better fleet reliability, fewer silent data quality failures, and clearer incident debugging paths. This is usually achieved through architecture refinement plus incremental implementation of high-impact changes rather than disruptive rewrites.
For full architecture detail, read the complete Rust IoT gateway deep dive.
Portfolio / Selected Work
Examples across telemetry pipelines, gateway software, streaming infrastructure, and architecture design.
If you are reviewing work samples in a similar technical area, Get in touch.
Green IT
My virtual power plant prototype consisted of a microservice-based data platform built using advanced technologies such as Apache Kafka, actor model programming in Scala, and Akka to leverage actors and advanced streaming.

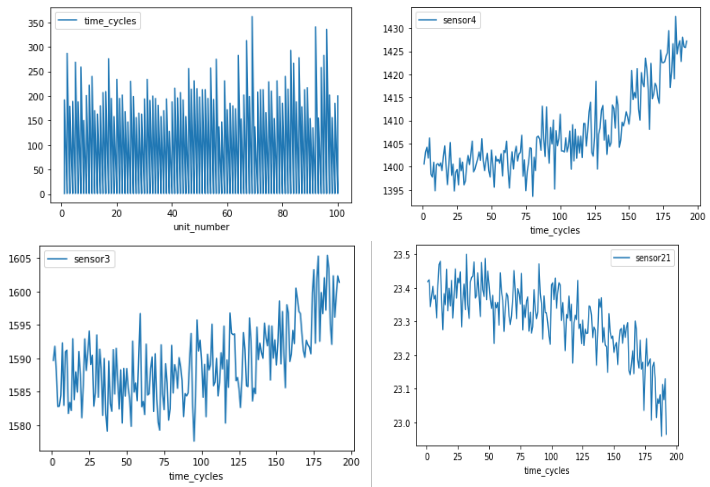
AI
This project focused on using deep learning for damage prognostics on aircraft engines. The project was part of a computer science course in artificial intelligence and deep learning.
Transport
This project was part of my final project for my Professional Bachelor’s degree in Software Development in January 2020, where I explored how data can be collected from vehicles and how such data can be used to improve safety and optimize the transportation industry.
If you are evaluating my background for a role, project, or technical conversation, these are the fastest paths into the relevant material.