Portfolio first
Start with shipped work, architecture context, and practical outcomes instead of business-style framing.
Denmark-based Software Engineer and Systems Thinker
I am Thomas Bonderup, a Denmark-based software engineer working across backend architecture, distributed systems, observability, and secure edge-to-cloud delivery. This site is a portfolio-first introduction to the projects, writing, and technical depth behind that work.
What to review first
Start with shipped work, architecture context, and practical outcomes instead of business-style framing.
Backend architecture, distributed systems, reliability engineering, and secure edge-to-cloud delivery.
Review the CV, inspect projects, read the writing, or reach out for a hiring or technical conversation.
Profile
Quick profile
MSc in Computer Science and Informatics
Rust, Scala, Java, Kafka, OpenTelemetry, and practical systems work across software architecture, reliability, and connected platforms.
My background combines formal computer science training with hands-on work across secure software, distributed platforms, and edge-to-cloud systems. I care about architecture decisions that remain understandable, maintainable, and operationally honest once real pressure arrives.
That means thinking carefully about service boundaries, observability, failure handling, transport security, and how teams keep momentum when systems become more complex than the original plan allowed for.
This site is meant to make evaluation easy: the CV provides the concise background, the portfolio shows concrete work, and the writing goes deeper on the engineering tradeoffs behind it.
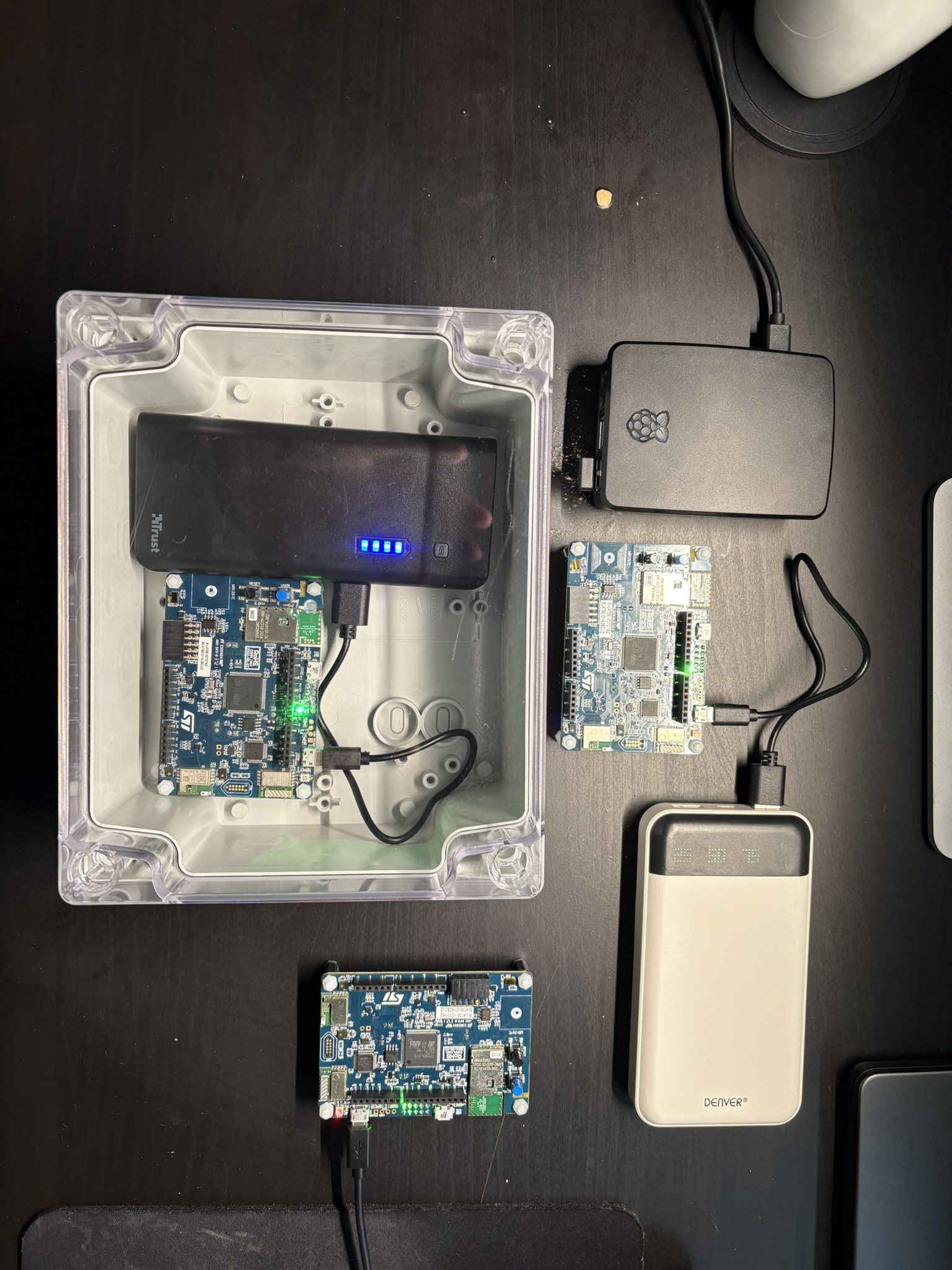
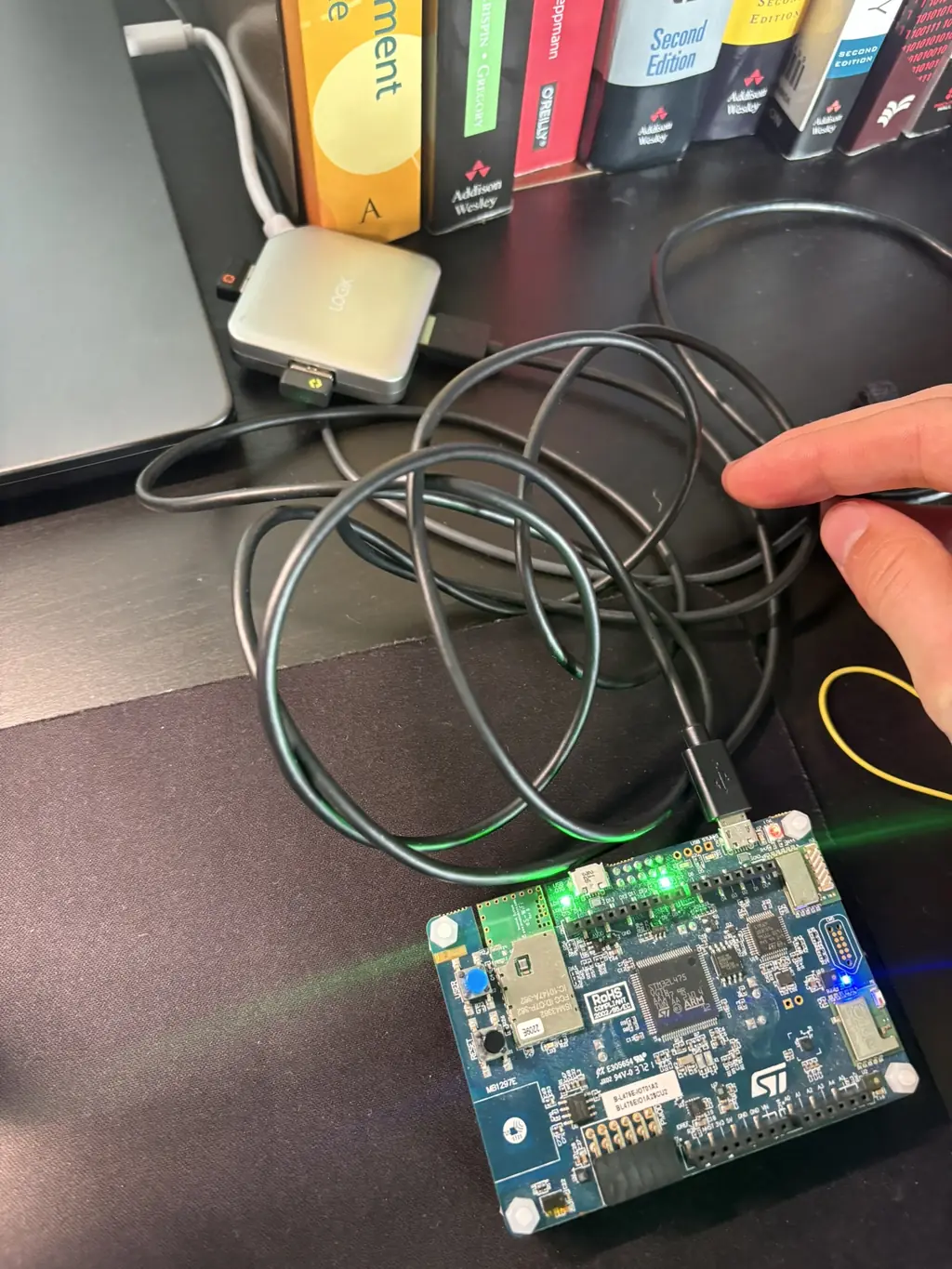
If you want the quickest technical proof trail, start with the Rust IoT gateway project, then continue into the architecture write-up.
Engineering Focus
Designing service boundaries, event-driven flows, data infrastructure, and production-ready delivery for complex software platforms.
Building and hardening gateways, telemetry pipelines, secure transport, and cloud integration for real-world connected systems.
Reducing incident pressure with stronger runtime behavior, debugging visibility, and technical decisions that hold up in production.
Portfolio / Selected Work
A proof-first view of architecture context, implementation choices, and technical outcomes.
If you are reviewing work samples in a similar technical area, Get in touch.
· 4 min read
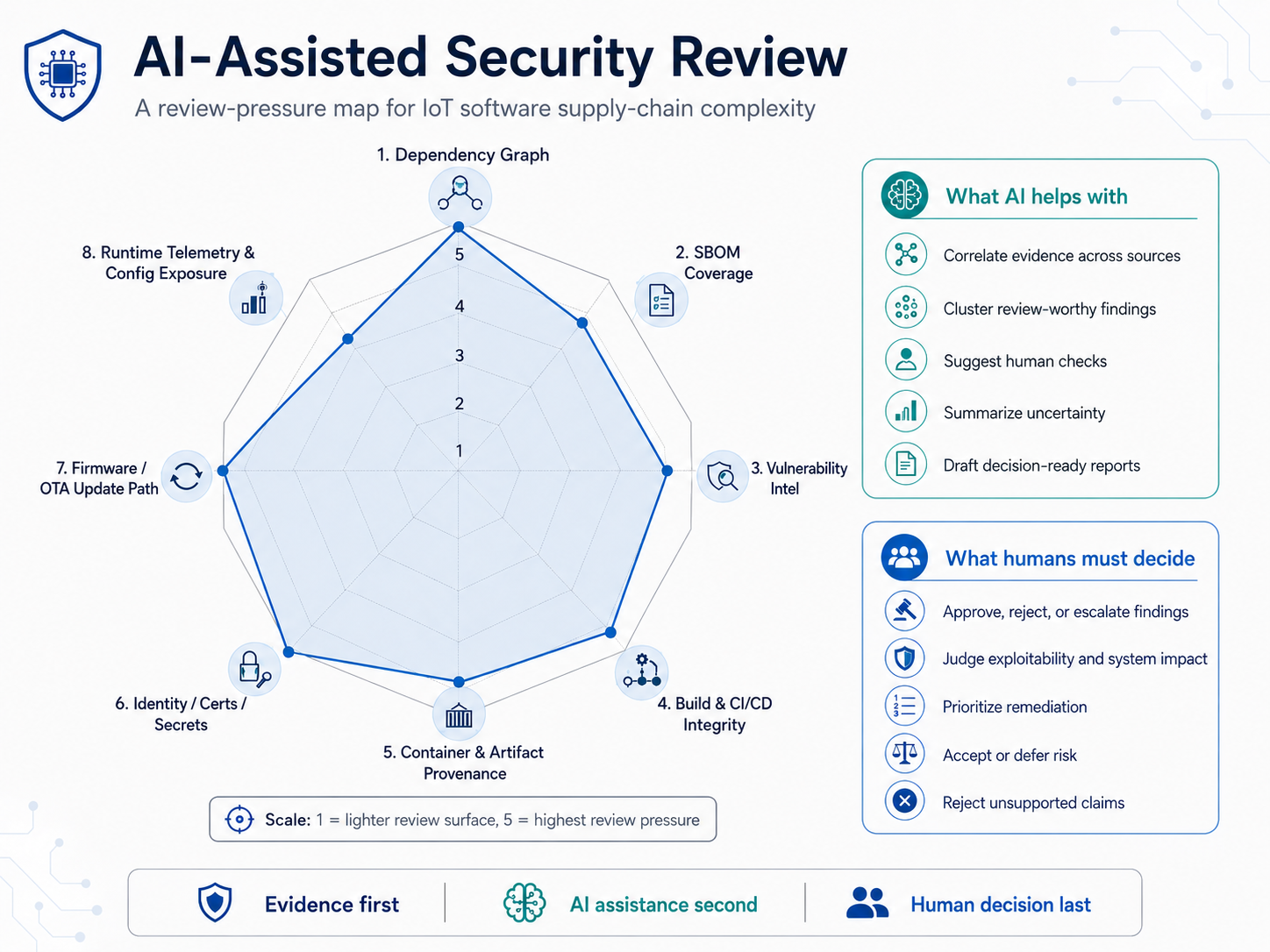
AI-Assisted Security Review
A local-first workflow for turning dependency, SBOM, and vulnerability evidence into human-reviewable security findings.

Certificate Lifecycle Control Plane
Java 21 Spring Boot API for IoT certificate lifecycle management with tenant-aware REST APIs, Keycloak JWT security, PostgreSQL/Flyway, Kafka outbox events, OpenAPI/Postman docs, and 88 tests.
IoT Security and Reliability
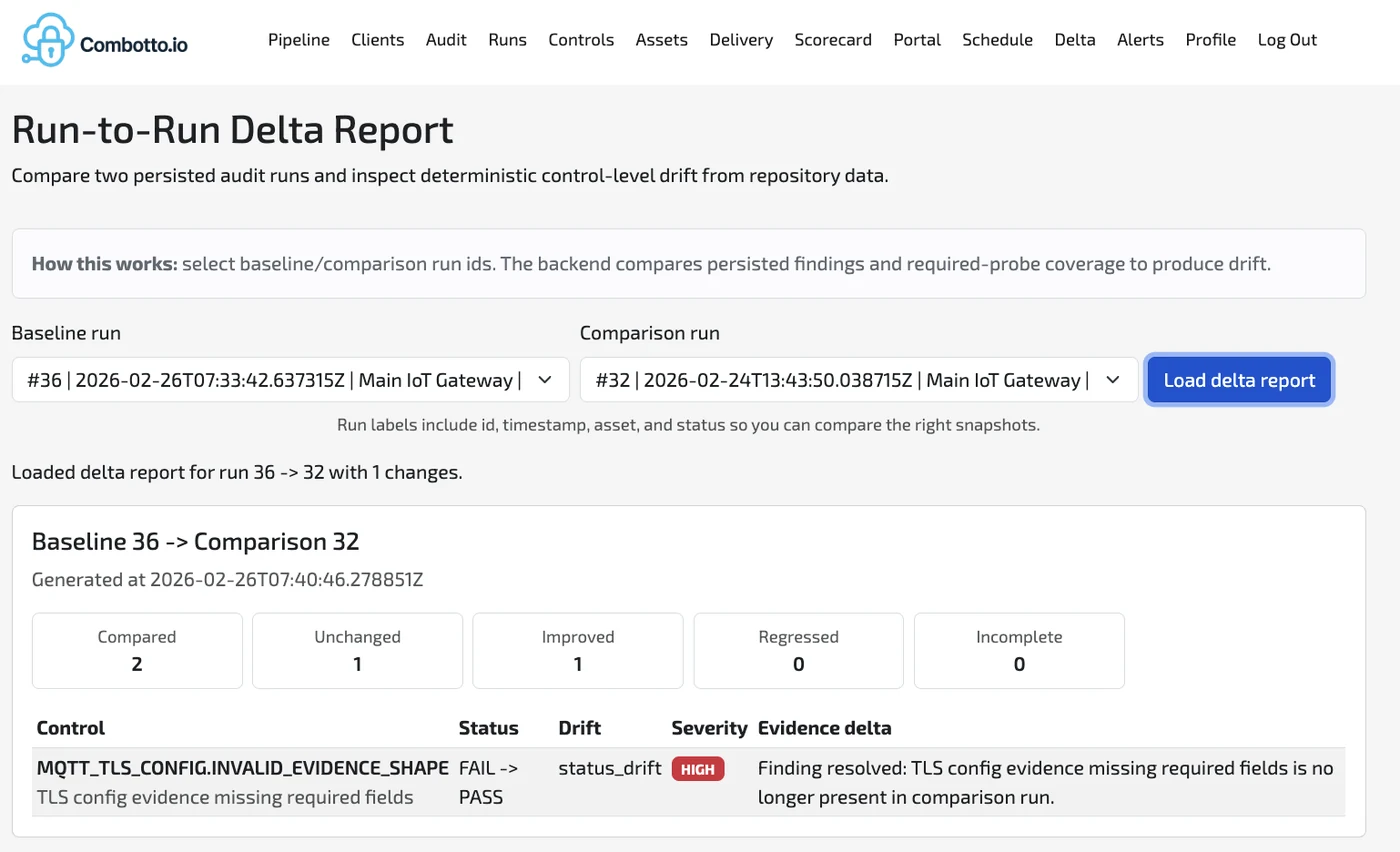
Built a repeatable audit engine for IoT systems that turns evidence into deltas, regression alerts, and an executable backlog that can be re-run in CI.
Engineering Writing / Notes
Technical articles that explain the reasoning behind architecture, reliability, and edge-to-cloud systems work.
If one of these articles overlaps with the systems or patterns you care about, Get in touch.
· 12 min read
Combotto.io is now live as the focused direction for my work in IoT, embedded software, and Rust systems programming. This post explains why that direction is a continuation of work stretching back through my thesis, earlier client work, embedded experiments, gateway engineering, and evidence-based audit tooling.
· 10 min read
This migration is not a full Scala-to-Java rewrite. The Scala/ZIO execution engine stays in place while a Java 21 + Spring Boot platform is built around it for control-plane workflows, integration, and long-term platform fit.

· 10 min read
I built an evidence-based audit engine with Rust probes and a Scala ZIO backend to automate evidence collection, evaluate versioned rules, and produce measurable security/reliability improvements over time.
Technical Depth
My work is hands-on across backend architecture, distributed systems, reliability engineering, security hardening, and production observability. I tend to focus on technical decisions that affect how systems behave in practice: service boundaries, failure handling, transport security, maintainability, and the visibility teams need when things go wrong.
In connected and edge-to-cloud systems, that often means gateway design, telemetry pipelines, protocol choices such as MQTT, gRPC, and HTTP, plus TLS and mTLS, retry and buffering behavior, and cloud integration on AWS or GCP. The writing and project pages on this site give a clearer view of those tradeoffs than a short profile summary ever can.
Hands-on work across backend architecture, distributed systems, event-driven integration, modernization, security hardening, and production observability. The focus is on boundaries, tradeoffs, and delivery choices that stay understandable when systems grow more demanding.
Practical engineering around IoT gateways, telemetry pipelines, transport choices such as MQTT, gRPC, and HTTP, plus TLS and mTLS, retry behavior, buffering, and cloud integration on AWS and GCP.
Linux-based delivery workflows, CI/CD, incident-ready visibility, and technical communication through architecture notes, articles, and implementation write-ups that make complex systems easier to reason about.
Next Steps
Get the concise version of experience, scope, and technical background.
See architecture, delivery constraints, and outcomes across selected systems work.
Go deeper on engineering decisions, reliability, and edge-to-cloud system design.
Contact
Reach out through the contact page if you want to discuss a hiring opportunity, compare notes on a system, or ask about work that overlaps with what you see here.